Several big conglomerate have been targeted by Ransomware Petya , including Russian steel and oil companies, Evraz and Rosneft , Danish shipping giant AP Moller-Maersk, Ukraine’s central bank, state power provider were among the infected. Ransomware per latest reports have affected more than 80 big organizations worldwide. Petya’s origin country is speculated to be Ukraine, from where the infection started.
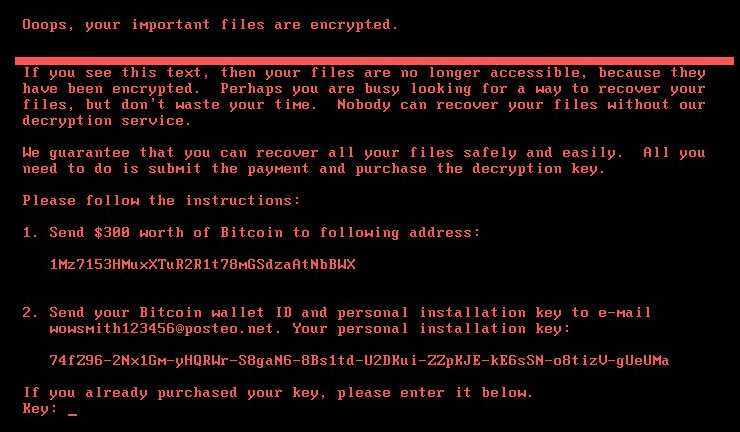
Petya Ransomware’s 300$ Demand
Petya Ransomware victims have claimed that after infection, Ransom ware in a message asks for 300$ in bitcoins to decrypt the encrypted files. Security experts have advised not to heed into ransomware demands and a fix is underway to restore the files.
Security Software companies vs Petya Ransomware ?
Some of the renowned security companies, including Symantec, Kaspersky and Avira have already released a patch to prevent infection of Petya Ransomware. Any communication about the recovery of already infected Petya Ransomware’s computer is awaited from any of them.
Ransomware Petya Origin and how does it exploit systems
Ransomware targets system with Eternalblue SMB vunerability , which is speculated to be exploited by United States National Security Agency for its use. Microsoft’s Operating systems which are not patched (MS17-010) can expect their systems to be targeted.
How to Protect yourself from Ransomware Petya, Prevent and Fix
Computer users using Microsoft operating system can patch their system as mentioned in ms17-010 security advisory
Already infected users with Ransomware Petya can run Symantec’s Norton eraser tool to clean it from the system. If it doesnt work , then symantec provides an option of running Norton Bootable recovery tool.
How to detect Eternalblue vunerability in a computer network
Metasploit framework is a security software for researchers and analysts usually used for vunerability assessment. You can also test waters , to check if any systems in your technology infrastructure can be attacked due to EternalBliss vunerability.
Step 1 : Download and Install metasploit or armitrage
Step 2 : Enter Metasploit Console by typing msfconsole command
Step 3 : Enter below commands with custom option
msf > use exploit/windows/smb/ms17_010_eternalblue
msf
msf > show targets
msf > set target TARGETOPTION
msf > show options
msf > set OPTIONNAME OPTIONVALUE
msf > exploit
Symantec said the latest #ransomware attacks used #EternalBlue, the same tool that was used in #WannaCry: https://t.co/9umOJW0b6j @NYTimes
— Symantec (@symantec) June 27, 2017
#Petya checks for preexisting infection by looking for its own filename,usually C:\windows\perfc.Creating this file may help as a killswitch pic.twitter.com/yh8O1v6CzB
— Security Response (@threatintel) June 27, 2017
Learn how #ransomware infects, spreads and attacks with our exclusive #whitepaper. https://t.co/tr0h5dNykD #infosec #protectmybiz pic.twitter.com/MTUQoFg6jb
— Kaspersky Lab (@kaspersky) June 28, 2017
#Petya is back with a vengeance: Even users who patched #WannaCry may be at risk but we’ve got your back! https://t.co/pCgZn0hOvY #infosec pic.twitter.com/jQulA3ZdWT
— Avira (@Avira) June 28, 2017